Risks of Multi-Accounting

Whether in the e-commerce sector, social media platforms, advertising placements, or affiliate marketing, multi-account operations have become a common operational strategy. However, the implementation of this strategy may face a neglected risk, that is, the leakage of browser fingerprints!
Browser fingerprints are unique sets of information composed of your device and browser settings. If you use the same device and browser while operating multiple accounts, then the browser fingerprints of these accounts will be identical. This could attract the attention of the platform, as it may be considered as brushing or fraudulent behavior, leading to account bans.
For example, on e-commerce platforms, sellers often create multiple accounts to increase product exposure and sales. However, if the browser fingerprints of these accounts are the same, they may be recognized as spam accounts by the platform, resulting in restrictions or bans. Similarly, on social media platforms, marketers also create multiple accounts to promote products or brands. If the browser fingerprints of these accounts are the same, they may be recognized as fraudulent behavior by the platform, thereby affecting marketing results and revenue.
Anti-Detect Browsers Are Not a Panacea
Even though many users have become aware of the risks of browser fingerprinting and have started using fingerprint browsers to mask their real device information, this does not mean that their accounts are completely safe. In fact, due to the different technologies used by different fingerprint browsers, or improper use, personal information may still be leaked, or a false browser fingerprint may be generated. This could lead to the user's device being marked as suspicious by the website platform, or multiple accounts being marked as associated.
Therefore, when using a fingerprint browser, users need to utilize a tool to:
- check if their browser fingerprint is authentic;
- see if the local real IP address will be leaked;
- compare the fingerprint of the fingerprint browser with the browser fingerprint of the real device;
- compare whether there are many repetitions in the browser fingerprints of different accounts.
After confirming the authenticity of the browser fingerprint, it is obviously safer to operate multiple accounts.
Using BrowserScan to Detect Browser Fingerprints
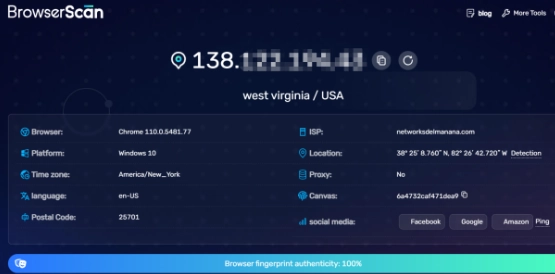
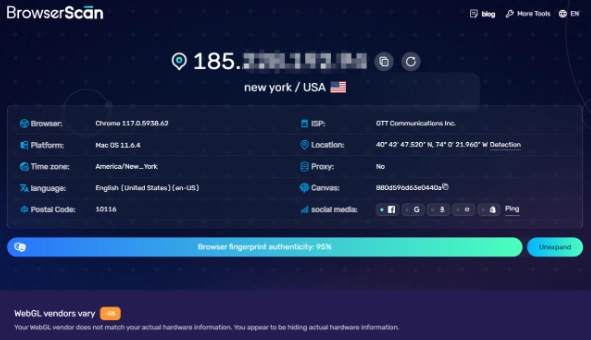
By accessing browserscan.net with a fingerprint browser or any other browser, you can understand the complete browser fingerprint just by waiting a few seconds.
Overview
In this section, you will check the authenticity of the browser fingerprint, giving you a rough understanding of the current browser fingerprint. The main information is as follows:
- IP address;
- postal code of the IP address location;
- geolocation of the IP address (Country, Latitude and Longitude);
- time zone of the IP address location;
- internet service provider of the IP address;
- browser version being used;
- operating system of the current device;
- whether a proxy server is being used.

If the authenticity of the browser fingerprint is only 90% or lower, then you need to continue to look at more detailed fingerprint information. (Values in Red Font are areas of deduction)
IP Address
BrowserScan will use WebRTC to detect if your real IP address will leak. This is because WebRTC can leak the user's real IP address. As shown in the figure, the IP address visiting BrowserScan is from the United States, but WebRTC leaked the real IP address (Singapore). In the eyes of some platforms, this user's behavior may be abnormal, especially on some social media platforms.
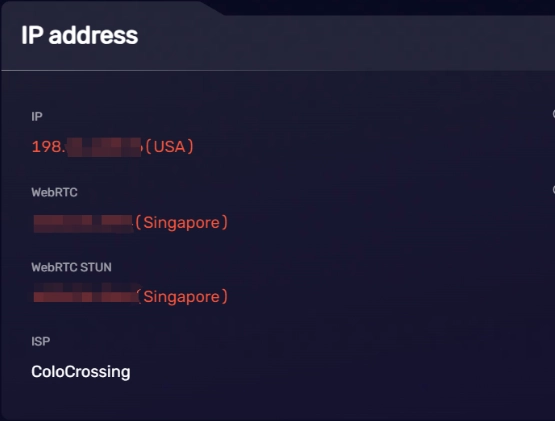
When you use an anti-detect browser, please be sure to check the IP address to see if WebRTC has leaked your real IP address.
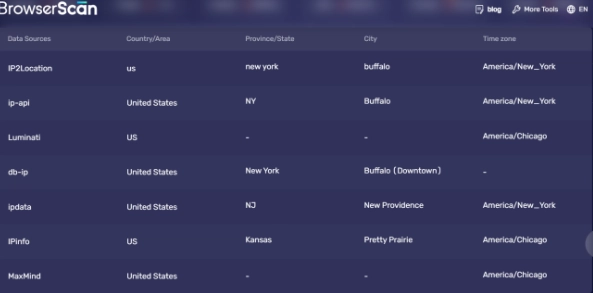
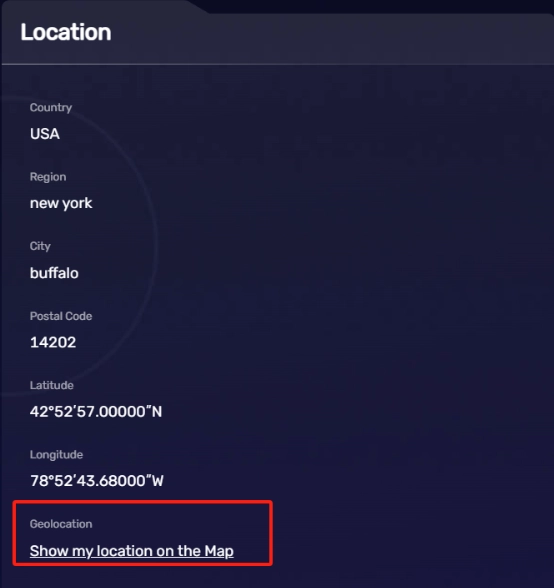
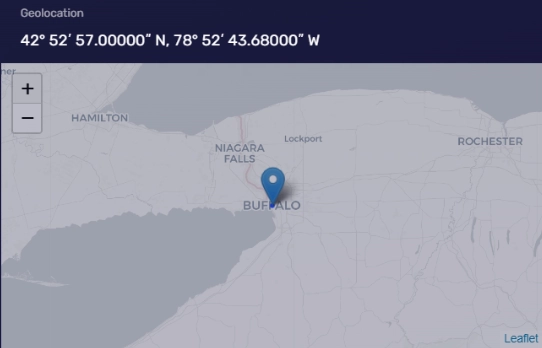
Geolocation
This part can understand the attribution of an IP address (country, state/region, city, postal code), latitude and longitude, and other information. If you need to understand more accurate geolocation, you can click "Show my location on the map" to view. (It can be displayed normally after allowing BrowserScan to obtain the current location information.)
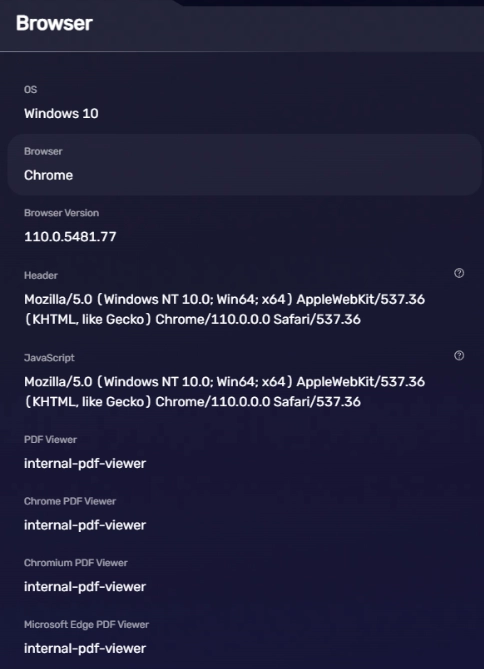
Browser
This part is mainly to view browser-related information, such as the operating system and version used by the current user, the type and version of the browser. The information about UserAgent, browser plugins, and other information.
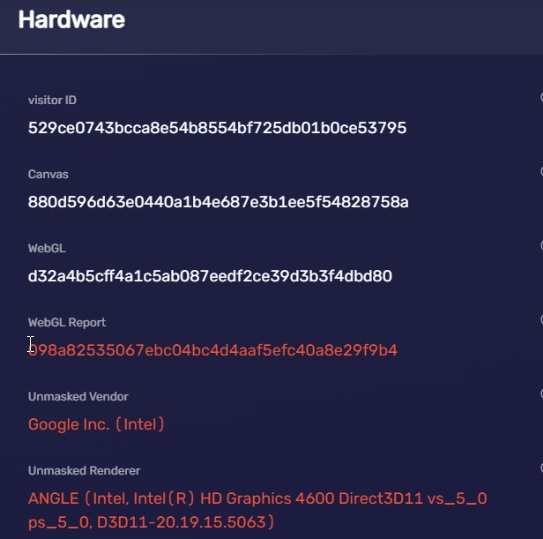
Hardware
This part is mainly to view hardware-related fingerprint information, such as GPU information, memory size, CPU concurrency, screen resolution, media device fingerprints, Canvas fingerprint, WebGL fingerprint, etc.
For example, when the fingerprint browser uses the UserAgent of Mac OS, if the fingerprint browser does not simulate the real Apple computer's GPU information, then the hardware fingerprint information will not match the UserAgent information. This kind of abnormal browser fingerprint will arouse the suspicion of the platform.
Software
The software part is mainly to view the timezone of the IP, check the local time of the IP address location, the language used by the browser, font fingerprint, whether Do Not Track, Cookie and other functions are enabled.
When an IP address is located in the United States, the timezone and local time should also be in the United States, not in other countries.
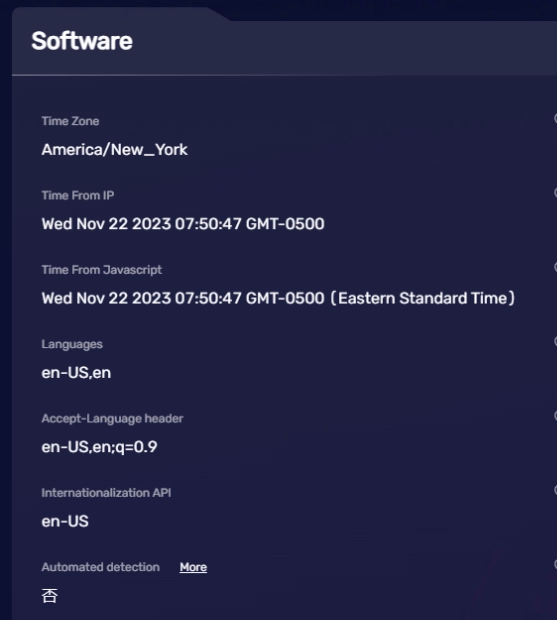
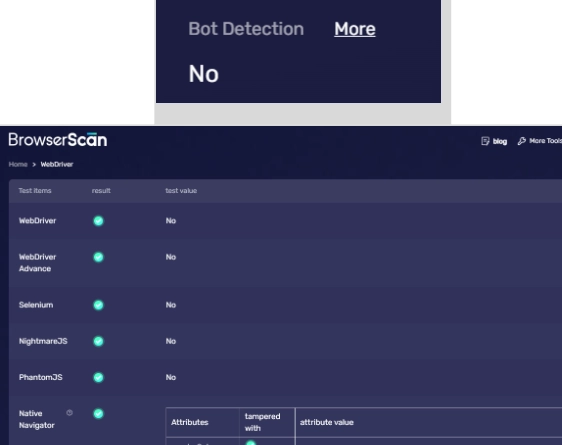
At the same time, if you are using automated scripts to control the browser, you should also check whether the browser behaves like a robot, because website platforms usually do not welcome "robot" visits. Use the automatic detection function of BrowserScan to see if the current browser has "robot characteristics".
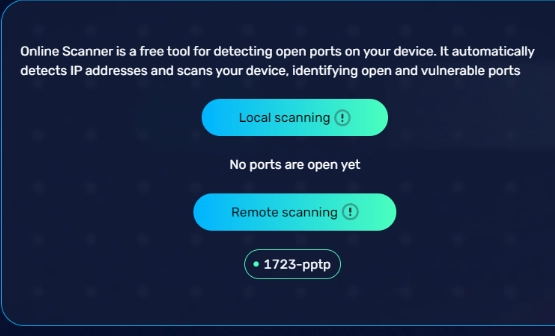
Port scanning not only risks exposing your personal information but also carries the risk of being hacked. You can use port detection to see if there are any open ports.
Other Tools
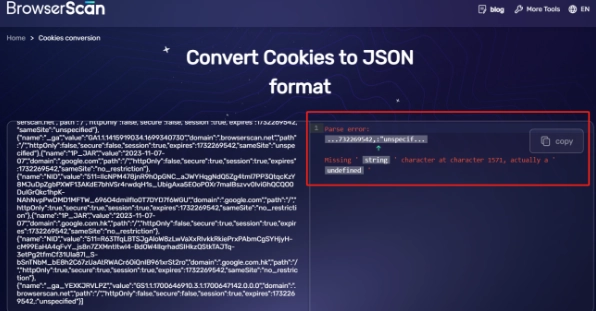
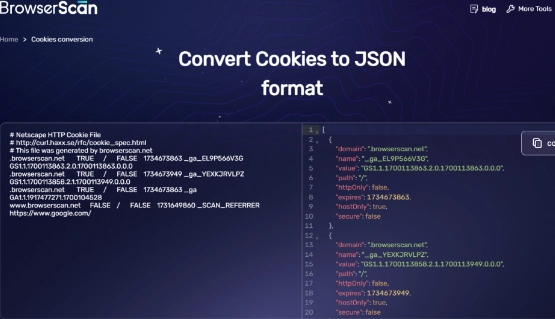
In addition to detecting browser fingerprints, BrowserScan also provides other tools. In the previous section, we introduced the automated detection tool and port detection tool. In addition, BrowserScan also offers IP address lookup and Cookie format conversion tools:
- IP Address Lookup. BrowserScan's IP address lookup feature includes seven major IP databases and can query the ownership information of an IP address in seven different IP databases. Due to database synchronization delays and differences, it is possible that the same IP address will yield different ownership results when queried in different IP databases. Therefore, when you are operating multiple accounts on a website, and the website is sensitive to changes in the IP address of the account, this feature can come in handy. If the proxy IP address used appears to have different ownership, then you might need to consider changing it.

- Cookie Converter. You can check whether there are any missing fields in the Cookie. BrowserScan supports converting Cookies from Netscape format to JSON format.

Conclusion
BrowserScan is constantly researching browser fingerprinting and continuously optimizing techniques to detect browser fingerprints. If you are currently using anti-detect browsers like AdsPower, Multilogin, Gologin, etc., you might as well use BrowserScan for a detection, just like doing a health checkup, to see if there are any abnormalities. Based on the abnormal information detected by BrowserScan, you can then use different solutions to solve these problems, thereby making your account environment more realistic and your account more secure.
In general, BrowserScan.net is a powerful browser fingerprints detection tool that can help you understand browser fingerprints and help you in protecting your personal privacy and network security.